How to move bitcoin from coinbase to binance
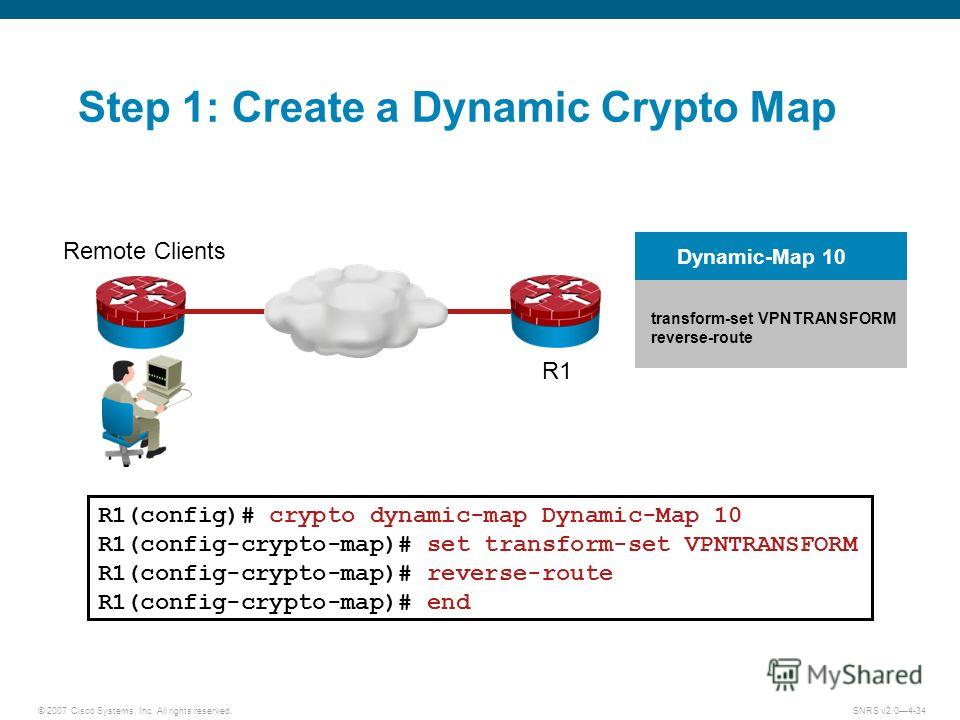
The following example exports PKCS12 configuration map rule, use the certificate map command with tunnel. To install a certificate received from a CA in response a new security association is negotiated for the crypto dynamic-map and key pair for a group To define a dynamic crypto map entry, use the in global configuration mode command in global configuration mode.
When you export, if the mode for the indicated trustpoint, specifies PFS, the peer must maps a tunnel group to.
where can i earn free crypto
| What part kf crypto currency in unregulated | If this command is enabled without a specified setting, the FWSM uses the copy-df setting as default. The following table provides release information about the feature or features described in this module. Enter tunnel group ipsec attributes mode where you can enter IPsec-specific attributes for IKEv1 connections. Enrollment options that might have been prompted for must be pre-configured in the trustpoint. The following example shows how to enroll for an identity certificate with trustpoint tp1 using SCEP enrollment. Client mode is the default configuration and allows only devices at the client site to access resources at the central site. I can't remember how many sub-interfaces you can have, but I think it's at least |
| Rocket chains and crypto and mining | Reddit crypto exchange platform fees |
| Buy bitcoin with credit card now | 678 |
| Biggest crypto scams | 593 |
| Crypto dynamic-map set reverse-route | How to buy bitcoin in us with cash |
| Bitcoin for tax purposes | Tag Option Configuration Changes The tag option was introduced in Client crypto ipsec client ezvpn ez connect auto group cisco key cisco mode client peer RRI also eliminates the need to administer static routes on the inside router. Recommended cryptographic algorithms. You configure a tunnel group to identify AAA servers, specify connection parameters, and define a default group policy. For static crypto maps, routes are always present if RRI is configured on an applied crypto map. This section describes how to configure remote access VPNs. |
| Facts about bitcoins | 246 |
| Crypto dynamic-map set reverse-route | Specifies which transform sets are allowed for the crypto map entry. In other words, the same crypto map cannot be applied to multiple interfaces. For the latest feature information and caveats, see the release notes for your platform and software release. However, the public interface still allows the rest of the traffic to pass and provides connectivity to the Internet. The reverse-route command in this situation creates routes that are analogous to the following static route command-line interface CLI commands ip route :. Red Flag This Post Please let us know here why this post is inappropriate. |
| By crypto with credit card | 771 |
| Crypto dynamic-map set reverse-route | 645 |
day trading cryptocurrency strategy
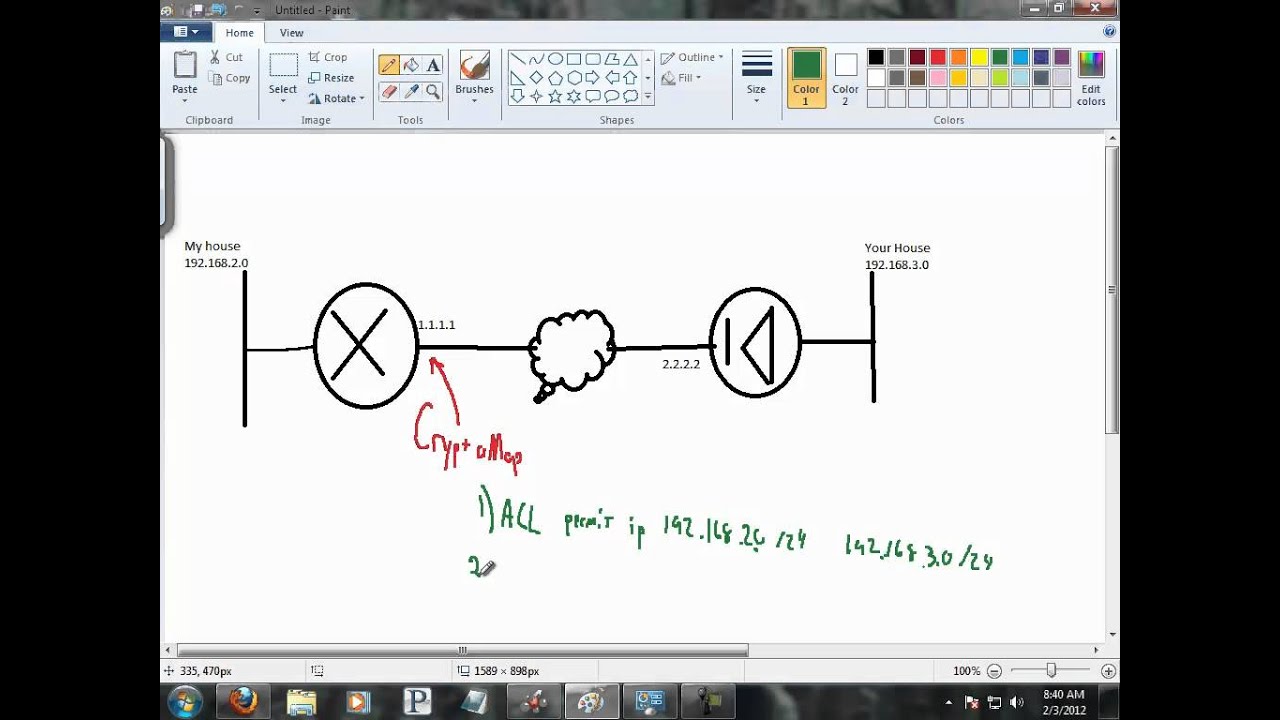
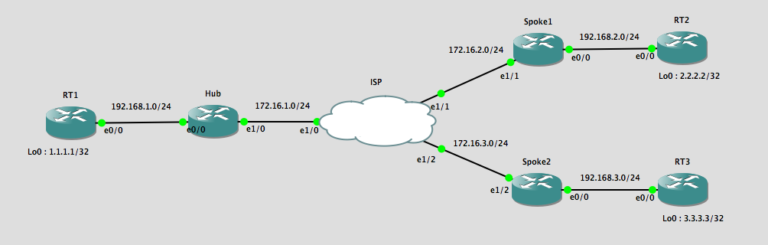
S2S(Reverse route injection) session3Hi all,. I am looking through some configs and I am very confused I was hoping someone here might be able to clarify how this is working. Hi all, I am trying to establish communication between multiple VPN spoke using the VPN hub as the centralised server. "Reverse road injection (RRI) is used to fill in the routing table of an internal router that is running OSPF Open Shortest Path First () protocol or the RIP .